2025 Top-20 Best CISO Blogs
Chronicles of a CISO has been ranked 8th of the Top-20 Best CISO blogs on Feedspot
Risk Preparedness in the Age of Policy Volatility
This panel discussion, as part of the Digital Risk North America virtual event, focuses on Risk Preparedness in the Age of Policy Volatility
The Virtual CISO Moment Interview
Virtual CISO Moment podcast with Greg Schaffer. We discussed the challenges facing SMBs when it comes to security and how we need to fix the model.
2025 Top-100 Best Security Blogs
Chronicles of a CISO has been named to the Top-100 Best Information Security blogs on Feedspot
The Compliance Equation: Preparing for Regulatory Shifts Under Trump 2025
This panel discussion, as part of the Digital Risk North America virtual event, focuses on the anticipated regulatory changes from the incoming Trump administration.
Inside Out: Unveiling and Mitigating Insider Threats in the Modern Workplace
A panel discussion, as part of the PrivSec Global event, that focuses on the complexities of insider threats, exploring the motivations behind them, detection methods and effective mitigation strategies.
Zero Trust Architecture: Implementing Best Practices in the US
This panel discussion, as part of the GRC World Forums Digital Risk US virtual event, focuses on implementing best practices for Zero Trust Architectures.
Compliance, Due Diligence, & More: Navigating Upcoming TPRM Trends
A discussion with Scott Lang, VP of Product Marketing at Prevalent, as we explore the emerging trends in TPRM and provide actionable insights to help you stay ahead of your…
Inherent Risk vs. Residual Risk: The Foundation of Effective TPRM
An on-demand webinar around effectively managing inherent and residual third-party risks and their importance for a durable third-party risk management (TPRM) program.
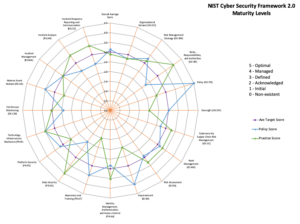
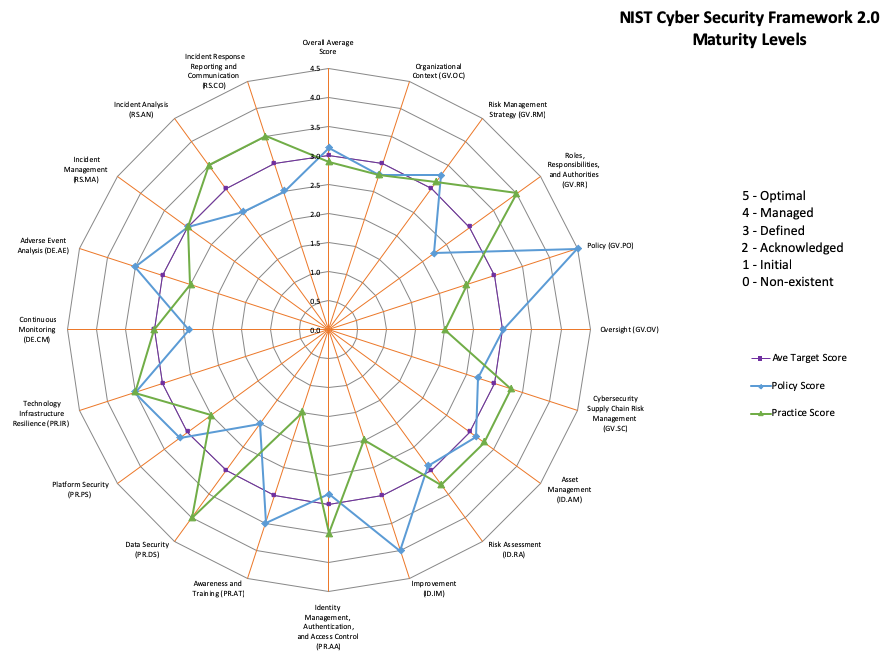
Updated NIST Cybersecurity Framework (CSF) Tool Released
The NIST CSF toolkit has been updated to reflect the new Cybersecurity Framework v2.0.
The Action That Shook An Industry
The SEC has put the executives of SolarWinds, including the CFO and CISO on notice. How will this impact the future of the security industry?
Technology Risk in the Private Equity World
New regulations and business drivers are forcing Private Equity firms to take a closer look at cybersecurity risk pre & post-acquisition.
A CISOs Guide to ESG
The term ESG has become a common parlance in the corporate world. How can a CISO leverage ESG to further their program and be better corporate citizens?
Cyber Resources For Veterans
Career and education resources for those on active duty or veterans who are looking to move into cybersecurity or S.T.E.M. careers.
The Evolving Game Of Cyber Insurance
Cyber insurance is increasingly difficult to obtain and more expensive than ever. A recent study identified the top 10 controls insurance carriers look for when determining coverage and cost. By…
The Interrupt-driven Life of a CISO
The interrupt-driven life of a CISO and how stress impacts our thought process and the changes we make to how our minds work.
Simplify Your Value Statement
In order to communicate their message quickly, Vendors need to develop a value statement that appeals to a CISO by quickly articulating how your solution reduces risk, minimizes staffing issues,…
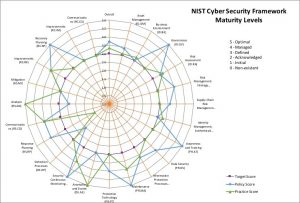
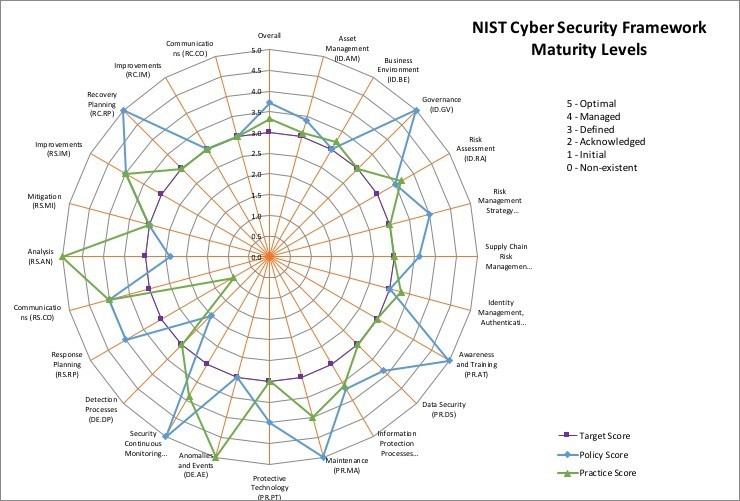
New Version of the NIST CSF Tool
Please note: Version 2.1 of the tool was uploaded to the site on February 28, 2022, due to a formula bug in the privacy worksheet. The NIST CSF Tool I…
The Problem With The Industry Analyst
Thoughts on the damage caused by Research Firms to the Information Security field and why the role of the Industry Analyst must change.
Millicom Builds Transformational Identity Security Program
The perimeter is dissolving. Employees are using any device from any location for work. With limited visibility from our traditional networking and endpoint security controls, how do we protect our…
New Resource: Industry Statistics and Metrics
A collection of information security metrics and statistic resources to use when discussing the state of information security. Many of the typical suspects are here – DDoS, Ransomware, SPAM, Insider…
Identity Management as a Foundation for Future-Proofing your Security
The perimeter is dissolving. Employees are using any device from any location for work. With limited visibility from our traditional networking and endpoint security controls, how do we protect our…
What if Identity Didn’t Exist?
The concept of Identity is critical to what we do. If it didn't exist, how would it change your approach and how would you answer the question?
Cybersecurity in the age of the pandemic
An interview with The Times (UK) around the need for an effective awareness and training program to manage the rapid growth of the remote workforce.