
Estimated Reading Time: 5 minutes
It’s hard to believe it’s been a year already. Twelve months ago, I took the leap and decided that it was time to start my own blog, and now, here we are celebrating the 1st anniversary. Over 110,000 visits later, I am shocked, honored, and above all, humbled that this little pet project has been so well received. And while the accolades have been wonderful, the truth is, the comments and emails I’ve received from the community have been truly inspirational.
And to all of you who have taken the time to visit, a most heartfelt thank you!
To be honest, I started the blog strictly as a place for my writings. LinkedIn really isn’t the publishing platform they claim to be, so after a few not-so-successful attempts there, I felt it was time to just bite the bullet and stand up my own little outpost on the intrawebbing of today’s world.
Over the past year, I’ve heard from vendors who love the transparency of my Open Letter To Security Vendors pieces to those (strongly) telling me how wrong I am about the NIST ID standards and colleagues who have appreciated some of the resources I’ve offered up. Through it all, the dialog has been engaging, encouraging, educational, and above all, inspiring.
Originally, I wanted to close out 2019 with some poignant diatribe about the state of our industry, but when the realization hit me about the first anniversary, I felt it was a bit more apropos to look back on the last year and recollect a bit about the journey and the engagement I’ve seen.
So, where to begin? Obviously where any security geek would…
Wait… Who’s Attacking Me…. and.. WHY?!?!
I guess the most obvious place to begin is the sheer number and complexity of the attacks the site is getting. In all seriousness, ignoring all of the script-kiddie scanners and rudimentary attacks being thrown at the site, I did not expect the types of daily attacks I’m seeing a year into it. I haven’t really publicized the site other than to you, my friendly and honorable colleagues; I don’t sell anything or collect credit cards; I don’t have medical data… nothing – It’s basically nothing more than a place for me to put a bunch of words.
That said, the complex URL’s, parameter strings, and ‘invalid inputs’ the site is being subjected to is pretty shocking. Not only are the type of attacks interesting, so is the location of the attackers. While I am not naive enough to believe some big foreign nation-state is trying to pwn my little site, the fact that three-quarters of the attacks come from adversarial countries is somewhat surprising. Now, if I’m being honest, I know that IP attribution doesn’t simply relate to attacker location, however, what intrigues me is the distinct difference between what I see here and what I see in my day job. I would expect to see far more US-based attacks than I am, which is the curious part.
I can hear some of you now… you’re a security guy – you should have expected it. While that’s a valid point, I equate it to how I feel watching a massive 777 take off – while I understand the science behind it, I am honestly still in awe when I actually see it up close. I know that virtually every IP on the ‘net is under attack, but to experience the barrage of attacks, and more importantly, have to defend against it in my ‘spare’ time, is still surprising when you consider what the site is actually used for.
As an aside, I wish I could submit the IOC’s I’m seeing to some open-source Threat Intel list. I’d have to imagine it would be worthwhile data. Any suggestions?
It’s All About The Content
With over 110,000 visits this past year, the real activity of the site has left me humbled and amazed. While I truly appreciate everyone who has emailed and commented, the popularity of some of the articles has caught me a little off guard as well. Posts that I didn’t think would gain much traction have exploded while those I thought would be beneficial to a wide audience didn’t seem to be. There were a few, however, that stood out above the rest. In no particular order:
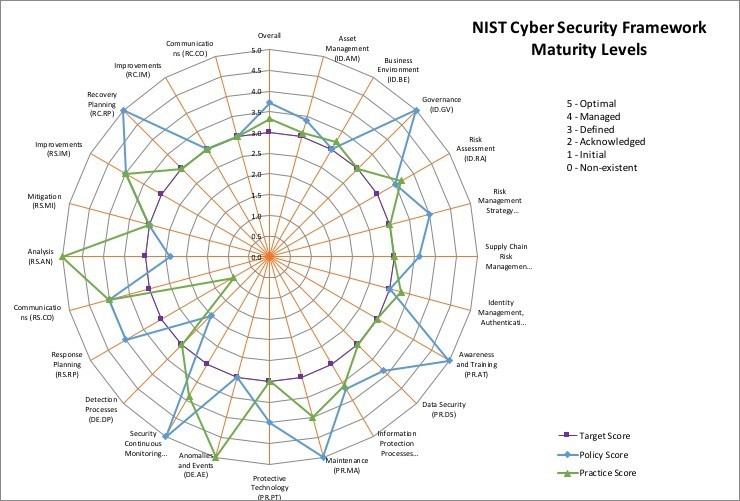
- NIST CSF Maturity Tool: Back January, I wrote a piece around the NIST Cybersecurity Framework and a tool I’ve used to measure compliance with it. The NIST CSF Maturity Tool is a fairly straightforward spreadsheet used to assess your security program against the 2018 NIST Cybersecurity Framework (CSF) standard. Not only was the piece the #1 read article on the site, but over 7,500 people have also downloaded the free maturity evaluation tool and are (hopefully) using it to better their programs.
- The Identity Catechism: The Identity Catechism is a series of 15 topics that were developed to provide anyone in the C-suite a fundamental understanding of what a mature Identity Management program looks like, what questions to ask, and some of the reasoning behind the need. It is not intended to be all-encompassing, nor fit every situation, but rather a general approach of what I’ve seen be successful. They go from basic to mature, with later questions being the most advanced practices. The IAM Maturity Evaluation Calculator was also released as a counterpart to the article as a way to measure the true maturity of an IAM program.
- My Daily Security Reading List: Without question, the one thing I am asked most these days is’ What do you read every day?’ Believe it or not, it’s not an easy question to answer. Beginning this past September, I began sharing my reading Daily Read each morning on the site, with so far, some pretty positive feedback.
- A Contrarian View of the NIST Digital ID Standards: Perhaps the main reason behind the majority of emails I’ve received is my taking NIST a bit to task on their ‘Digital ID Standards’, which frankly has evoked a lot of passion on both sides. At the end of the day, the general consensus of opinion from both sides is that passwords are a major weakness that needs to be addressed, but the mistake of taking a singular point out of context is doomed to failure. One must either implement all of the Digital ID standards, or stick with what you have, but don’t selectively pick parts of the standard you like to make yourself look…. Progressive.
A Final Thought
In any effort like this, there will always be people in the background who have been there from the beginning. Your guidance and assistance helped me early on with ideas, design, proofreading, and feedback. You all know who you are and I truly hope you take as much pride in what this has become as I do.
Finally, I’d like to thank all of you who have sent me notes of support and encouragement over the last year. I sincerely appreciate every note, comment, and ‘like’ that each of you makes time for. Your words of encouragement have truly helped in those days I didn’t feel like writing, and for that, I will be eternally grateful.
Copyright © 2002-2025 John Masserini. All rights reserved.


Congratulations John on your first anniversary of Chronicles of a CISO. I am confident that there will be many more celebrations to come for the great work that you are doing.
Thank you Marci!
Echoing Marci McCarthy’s sentiments above, congratulations on your first ‘Chronicles of a CISO’ anniversary! I have found your curated list of ‘Must Reads’ list to be of particular value.
Thanks again John for sharing your unique vantage point with the broader community.
Sincerely,
Eugene